How To Remove Binary Options Virus Off Computer

Curt on time? Here's how to remove the COM Surrogate virus:
- one. Scan Device — Run a total organization browse with a high-quality antivirus (Norton is the best).
- 2. Remove Virus — Afterwards the scan is complete, let the antivirus remove all instances of the COM Surrogate infection.
- 3. Stay Protected — Protect yourself from further infections with a high-quality internet security packet (again, Norton is the all-time).
COM Surrogate is a normal Windows process, just hackers use fake versions of it to infect a PC while avoiding detection. The COM Surrogate virus is one of the most common malware infections on Windows computers — it'southward pretty unsafe, but getting it off of your PC actually isn't very hard.
However, you should never try to delete the COM Surrogate virus manually.If you attempt to remove the virus manually,y'all risk causing permanent damage that tin can lead to Windows 10 failing completely.
The most efficient and secure style to remove the COM Surrogate virus is by installing a comprehensive antivirus suite. A skillful antivirus will non merely quarantine and remove every example of the COM Surrogate infection from your computer, simply it will also ensure yous remain prophylactic from hereafter threats with its real-time protection and scanning capabilities.
60-Days Hazard-Free — Attempt Norton Now
Preliminary Step: Checking for a COM Surrogate Infection
This stride is for advanced users who want help in understanding malware diagnostics. If you simply want to remove the COM Surrogate infection (and other malware), skip ahead to learn how.
If y'all desire to check whether the COM Surrogate process running on your system is malware, you lot must first sympathise what the standard COM Surrogate process is.
COM is an acronym for Component Object Model and is related to dllhost.exe in your System32 folder . In simple terms, information technology's a binary interface that communicates with different software and increases the software's capabilities. For instance, when a folder on your Bone needs to draw thumbnails, it volition request COM Surrogate to do merely that. This is why COM Surrogate is referred to as "middleware".
COM Surrogate is a pathway between applications, commands, and your operating system. It's important for your computer's everyday functioning. This is why hackers ofttimes disguise malware as middleware — they want to get access to your entire arrangement.
That said, hither's how to know if you're looking at an accurate instance of COM Surrogate or a unsafe piece of malware:
Bring upwards your Task Managing director past hit CTRL + Shift + ESC.
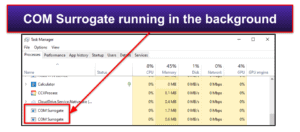
In the picture above, you lot can run into COM Surrogate is running twice on the system. While this may look alarming, it'southward not. It only ways multiple applications are using the middleware to assist them in communicating with the OS.
To confirm this, you lot can right-click on both instances and click Open File Location. If they go to a file called "dllhost.exe" in the System32 folder on the system, and then information technology is unlikely they are malicious.
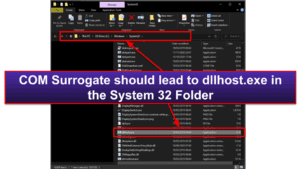
If the file is located anywhere other than dllhost.exe, then you accept a virus and should follow my removal steps.
Stride 1. Identify the COM Surrogate Virus With Your Antivirus (And Don't Make the Problem Worse!)
Important : Do not connect your cell phone, tablet, or USB drive to an infected calculator. In doing so, y'all risk the virus replicating itself onto those devices.
In one case you lot've downloaded a secure antivirus program, run a full deejay browse on your computer. Even if you call back you know where the infection started or you know where the suspicious .exe file is located, a full disk scan is best.
A full disk browse will find, quarantine, and remove every copy of the COM Surrogate virus, also every bit ensure that your device isn't infected with whatsoever other malware, including spyware, rootkits, or worms that can often run undetected.
Call back: Run the full organization scan until it's finished. DO Not abolish the scan when y'all see the virus appear on the infected file listing. There'due south no manner of knowing how many other copies of it exist in your organisation.
The total scan can take anywhere from 1–iv hours, so sit tight because your antivirus needs to analyze every unmarried file and procedure on your computer.
When your antivirus has alerted you that the scan is complete,every example of malware on your system will be identified and quarantined — including the COM Surrogate virus.
60-Days Risk-Free — Try Norton Now
Step 2. Remove the COM Surrogate Virus Infection and Delete Any Other Infected Files
When your antivirus has identified and quarantined all of your compromised files, it will requite you the option to delete them. Advanced users tin can go through the quarantined files and brand sure there are no fake positives before hitting the Delete push. But most users volition only desire to trust their antivirus software — if it's been flagged every bit malware by a plan like Norton, chances are y'all don't desire it on your device.
After you lot've removed all of the compromised files from your system, it's a good idea to restart your computer. Afterward you lot restart your device, run a second full deejay browse to ensure your antivirus has removed all traces of the COM Surrogate infection. This may not take as long during the 2d scan — many antiviruses, including Norton, call up which files they have already scanned and are able to analyze your deejay much more than rapidly after the first full deejay scan.
As earlier, be certain to let your antivirus finish its 2d scan. Once the browse is finished, and you've reviewed and deleted all of the compromised files in your quarantine, you tin breathe a sigh of relief. Your device is 100% malware-free! For now…
Even though y'all've finished removing the COM Surrogate virus, there are still thousands of malware files out there that can infect your devices, compromise your online accounts, and spread through your Wi-Fi network.
60-Days Run a risk-Complimentary — Try Norton Now
Step 3. Go along Your Device From Getting Re-Infected
Since the COM Surrogate virus has infected you lot once already, y'all've witnessed first-hand just how easy it is to get malware on your PC. New malware is released every day, and at that place'due south also the gamble of online data harvesting, identity theft, and public Wi-Fi hackers.
In today'southward online earth, how can y'all keep your devices and information prophylactic? There are several things you tin practice:
-
Proceed Your Software, Os, and Drivers Upwards-To-Engagement
When developers find vulnerabilities in their software that are existence exploited past hackers, they patch those vulnerabilities and transport the patches to users in the class of software updates.
Software updates can be annoying, but they are essential to keeping your computer safe from the latest malware threats.
However, with the corporeality of devices, apps, and programs that most users are running these days, it tin be actually hard to go along track of which programs demand to be updated. One slap-up tool comes from the antivirus provider Avira — it lets you browse your PC for out-of-date software and automatically update it.
It'south also incredibly of import that you stay on the latest operating system and keep your drivers updated.
When an operating arrangement ages, developers will stop supporting information technology. And so any vulnerabilities won't be fixed with updates. This means that older operating systems grow more and more than vulnerable every day as hackers continue to develop tools to infiltrate them.
Most operating systems and programs have an auto-update option. Wherever possible, select this option to make sure yous're keeping all of your devices and organisation drivers up-to-date.
-
Don't Download Suspicious Files
Whether information technology'due south from an e-mail or a suspicious website, don't download files unless you're 100% sure you recognize where they're coming from. The vast bulk of malware is delivered with seemingly legitimate free software or it's fastened to deceptive emails — if you lot don't put malware on your figurer, it's very hard to go infected.
Your antivirus can help with this by scanning emails and tagging suspicious files, plus scanning all downloads before they can make changes on your reckoner. Withal, it'southward still all-time to practice common sense and avert files from unknown sources.
-
Secure Your Wireless Network
Make sure your wireless network is secure before you go online. You lot tin can practise this by using a firewall, but you should likewise ensure your dwelling house Wi-Fi connection is password-protected, as well.
You tin can see if a connection is countersign-protected by looking in your network list — the ones that aren't countersign-protected have a warning sign adjacent to them.
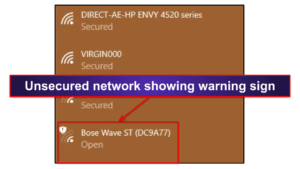
Unsecured networks are far more vulnerable since anyone tin connect to them, but hackers tin infiltrate a secured network, too.
Nearly people don't think to prepare their Wi-Fi router's password, and the default router countersign ends upwardly beingness something like "countersign". This is a very easy password to guess, and hackers estimate these weak passwords and break into "password-protected" networks all the time.
To set a countersign for your home router, you will need to log into your router'southward settings on a web browser and follow the instructions provided. When you lot purchased your router, you should have received instructions explaining how to do this. If not, endeavour typing the router'due south model number into Google.
Quick Tip: A safe password should be at least 15 characters long and utilise a random mix of messages, numbers, and special characters. You can utilise a password manager such as Dashlane to store all of your passwords, so you lot won't have to worry near remembering your router'south password.
-
Download a Secure Antivirus Programme
There are a ton of antivirus packages on the marketplace. However, there are but a few that are truly excellent, providing all of the security protections that you need to stay safe online. You lot can bank check out 2022's best antivirus packages here.
I really like Norton 360 — information technology'due south a premium antivirus suite with one of the all-time anti-malware engines in the world, along with a ton of useful security protections. Norton's antivirus scanner uses artificial intelligence, advanced heuristics, and a massive malware database to go along malware off of your device.
Norton also includes:
- Anti-phishing protection — Flags suspicious websites and protects you from online scammers.
- Firewall — Blocks hackers from entering your network.
- Virtual private network (VPN) — Keeps your cyberspace usage anonymous, preventing network attacks, web surveillance, and man-in-the-heart attacks.
- Parental controls — Protects children by using content filters, app and screen fourth dimension schedules, YouTube monitoring, and even location tracking.
- System cleanup — Gets rid of junk files and increases system performance.
- Password manager — Stores, generates, and auto-fills passwords, so hackers can't steal them.
- Identity theft protection (US only) — Monitors credit reports, the dark web, and breach databases for compromised accounts, and includes a $ane million insurance policy.
threescore-Days Chance-Gratis — Try Norton Now
Can I disable COM Surrogate?
You lot can't disable COM Surrogate. Information technology'southward a core system function within Windows that will be called upon every time an application requests it.
I actually tested this past opening the Chore Manager on my reckoner and clicking "End Chore" on every instance of COM Surrogate. I so opened a binder in File Explorer and switched to Thumbnail View. As soon as I did this, COM Surrogate once again appeared on my job listing.
This is normal, and it shouldn't be interfered with. COM Surrogate is a function of dllhost.exe's role and a required Windows background process.
If in doubtfulness, follow this guide on how to remove malicious instances of COM Surrogate.
Why does COM Surrogate go along crashing?
It's totally normal for COM Surrogate to crash occasionally. COM Surrogate is a sacrificial process. In fact, surrogate means to "human action in another's place".
For case, when you open a binder and switch to Thumbnail View, Windows fires a COM Surrogate to draw those thumbnails within File Explorer. If, for whatever reason, this process crashes, instead of having the entirety of File Explorer crash, only COM Surrogate volition crash.
In other words, COM Surrogate crashing is aform of protection.
That being said, consistent crashes or system slow-downs may be the symptom of something more serious. Should COM Surrogate crash frequently, follow the in a higher place steps. Your reckoner may be infected.
Where is COM Surrogate located?
COM Surrogate is an internal procedure that is initiated past dllhost.exe — which is located in your System32 binder*.
COM Surrogate itself isn't something you can notice in your system files. Therefore, if you do come across "COMSurrogate.exe" or anything similar, your estimator is probably infected with malware and you should check out the rest of my instructions for how to remove it.
*For the less tech-savvy users, the System32 binder is where Window's most important .EXE and .DLL files are located. If you were to delete System32, Windows would no longer role.
Why is the COM Surrogate virus unsafe?
The COM Surrogate virus is dangerous considering it tin can open a backdoor into your system. Hackers can utilize that backdoor to intermission into your calculator and steal sensitive information. This tin include:
- Usernames
- Electronic mail addresses
- Passwords
- Banking company account details
- Credit card information
The hacker volition even be able to use the backdoor to download more than malware onto your organization. Trojans can also be used to hijack your operating organisation for botnets and cryptojacking malware. That's why it'southward imperative that yous remove all instances of the COM Surrogate virus, and any other malware that may have infected your arrangement. If yous don't know how to remove a virus from your PC, and then cheque out the rest of my guide for removing COM Surrogate from your computer.
About the Author
How To Remove Binary Options Virus Off Computer,
Source: https://www.safetydetectives.com/blog/how-to-remove-com-surrogate-virus-easy-steps/
Posted by: matlockwousidersing.blogspot.com



0 Response to "How To Remove Binary Options Virus Off Computer"
Post a Comment